We may earn a commission when you buy software.
The 5 Best Antivirus for Android Phones (2026 Update)
Updated: December 2025

By: Tibor Moes is the founder of SoftwareLab. He has tested 28 antivirus brands and studied Cybersecurity at Stanford. Read how we test antivirus.
Norton Antivirus
Ranked #1 of 28 for Android
- Malware Protection 100%
- Security Features 100%
Norton has the best anti-malware protection, excellent security features, and a great price. It’s the best antivirus of Android.
- Malware protection: 100%. Norton stopped all 1,200 malware attacks in our test.
- Security features: 100%. Anti-phishing, VPN, app security, scam protection, and more.
- Speed impact: 100%. Norton did not slow down our test phone.
Try it risk-free, thanks to its 60-day return policy.
Kaspersky Antivirus
Ranked #2 of 28 for Android
- Malware Protection 100%
- Security Features 100%
Kaspersky offers excellent protection and security features for Android, but it’s quite expensive compared to Norton.
- Malware protection: 100%. Kaspersky stopped all 1,200 malware attacks in our test.
- Security features: 100%. Anti-phishing, VPN, password manager, and more.
- Speed impact: 100%. Kaspersky did not slow down our test phone.
Try it risk-free, thanks to its 30-day return policy.
The best antivirus for Android
We tested 39 antivirus apps from 28 brands, infecting our test phone with 1,200 malware samples to evaluate their protection capabilities. We also examined additional features such as password managers, anti-phishing tools, and VPNs.
Here are the best antivirus for Android:
- 🥇 Norton Antivirus – The #1 in 2026
- Kaspersky Antivirus
- McAfee Antivirus
- Bitdefender Antivirus
- Panda Antivirus
Scroll down for the reviews.
Norton Review

Norton is #1 of 28 apps for Android.
It includes all essential features:
- Anti-malware
- Web protection
- Identity theft scanner
- Unlimited VPN
- Genie scam protection (new)
And a range of bonus features:
- App advisor
- Wi-Fi scanner
- Vulnerability scanner
- Anti-tracker
- SMS security checker
Most importantly, the VPN doesn’t have a data limit. By contrast, many other antivirus apps have a VPN data limit of a few hundred MB / day. That’s not enough.
When you frequently surf on public Wi-Fi, Norton’s unlimited VPN will protect your privacy on those unsecured networks.
We highly recommend Norton for anyone who surfs, shops, or banks on their phone.
Try it risk-free, thanks to its 60-day return policy.
Detailed Review
Norton Antivirus for Android Review
Security Features
During our tests, Norton’s Android app impressed us with its comprehensive protection suite presented in a clean, easy-to-navigate interface. The central “Scan Now” button enables quick malware checks, while the app’s key features deliver extensive, layered security:
- App Security: Norton’s App Advisor is the standout feature. It evaluates apps both before and after installation, warning about malware, privacy risks, or intrusive advertising. This proactive approach ensures users only install safe, trustworthy applications.
- Internet Security: With the Safe Web Browser and Norton Safe Search (powered by Ask.com), we were protected from phishing sites and malicious downloads while browsing the web.
- Wi-Fi Security: The app automatically scans Wi-Fi connections, identifying unsecured networks and weak passwords. It provides real-time alerts when connecting to risky public hotspots.
- Device Security: Norton scans for unsafe configurations such as untrusted certificates or outdated system software that could create vulnerabilities.
- SMS Security: It analyzes incoming text messages for phishing links or other malicious content, preventing common social engineering attacks.
Privacy Features
In our experience, Norton’s privacy tools provide strong protection for users who frequently connect to public networks or value data anonymity:
- VPN: Norton’s built-in VPN offers unlimited, encrypted browsing with no data caps. It effectively hides the user’s IP address and prevents online tracking, making it ideal for safe browsing on public Wi-Fi.
- Ad Tracker Blocking: The tracker blocker prevents websites and advertisers from collecting personal browsing data, improving privacy and often speeding up page loading times.
Identity Protection Features
Norton extends its protection beyond the device with Dark Web Monitoring, which continuously scans dark web sources for personal information such as email addresses, driver’s licenses, and financial records. Although this feature isn’t directly accessible within the Android app, users can manage it through Norton’s website or the Norton LifeLock Identity app for enhanced protection against identity theft.
Norton Mobile Security vs. Norton 360
- Norton Mobile Security: Best suited for users seeking reliable, single-device protection on Android. It includes all essential security and privacy features at a reasonable price.
- Norton 360: Designed for those managing multiple devices across platforms. It includes all Mobile Security features and adds advanced tools such as a password manager and a VPN with customizable server options.
Is Norton the Best Antivirus for Android?
Based on our hands-on testing, Norton ranks among the best Android antivirus solutions available. It combines powerful protection with an unlimited VPN and a smooth user experience. Although it no longer includes anti-theft tools, its overall performance, reliability, and usability make it an outstanding option.
For Android users protecting a single device, Norton Mobile Security is a smart, dependable choice. For users seeking broader, multi-device protection with extra features, Norton 360 provides superior versatility and value.
Kaspersky Review
#2 of 28 antivirus for Android

Kaspersky is #2 of 28 apps for Android.
Kaspersky is one of the best Android antivirus apps that we’ve tested. And with the launch of Kaspersky Plus and Premium, Android users can get the unlimited VPN as well.
It covers all the core features, including anti-malware, web protection, anti-theft tools, an identity theft scanner, a VPN, and a range of bonus features. These include a call filter, safe messaging, app lock, settings scan, parental controls, and app permissions scan.
However, to access the unlimited VPN and password manager, you need to sign up for Kaspersky Plus. Which is an expensive product compared to Norton Mobile Security for Android.
Try it risk-free, thanks to its 30-day return policy.
Detailed Review
Kaspersky Antivirus for Android Review
Security Features
In our testing, Kaspersky’s Android app delivered a powerful blend of security, privacy, and usability. The app provides layered protection against both digital and physical threats through a clear, well-organized interface. Its main features include:
- Scan Options: Kaspersky offers three flexible scan modes—Quick, Full, and Custom. Quick scans focus on the most vulnerable areas of the system, Full scans perform a deep analysis of all files and apps, and Custom scans allow users to target specific folders. Each type runs efficiently and accurately detects malicious software.
- Update Feature: Users can manually refresh the malware database to ensure the latest threat definitions are applied. Following each update, the app automatically runs a quick scan to catch any new risks immediately.
- Real-Time Protection: Kaspersky’s real-time protection continuously monitors for threats, including adware, and provides instant alerts if any suspicious activity is detected.
- Call Filter: The built-in call blocker effectively filters out spam and unwanted calls, improving privacy and reducing distractions.
- Anti-Theft Tools: This is one of Kaspersky’s strongest areas. Users can remotely lock, locate, or wipe their device, trigger an alarm, or take a “mugshot” of the thief—ensuring data remains secure if the phone is lost or stolen.
- App Lock: Sensitive apps such as banking or messaging platforms can be locked behind a PIN or password for added protection.
- Safe Messaging: The app scans incoming SMS messages for phishing links or malicious URLs, preventing common scams before they reach the user.
- Internet Protection: The integrated browser protection blocks phishing pages, trackers, and malware-hosting websites to create a safer browsing environment.
- Data Leak Checker: This feature scans the dark web for compromised credentials—such as emails, usernames, or passwords—and alerts users if their data appears in a breach.
- Weak Settings Scan: Kaspersky evaluates the device’s security settings, identifying weak configurations and offering actionable recommendations to strengthen protection.
- My Apps: This privacy-focused tool reviews all installed apps and highlights those requesting access to sensitive data, giving users clear control over their privacy.
- VPN: The included VPN encrypts internet traffic, hides the user’s IP address, and enables secure browsing on public Wi-Fi networks.
- Password Manager: Available as a standalone app or bundled with Kaspersky Security Cloud, this feature stores and generates strong, unique passwords to safeguard online accounts.
Is Kaspersky the Best Antivirus for Android?
Based on our in-depth evaluation, Kaspersky ranks among the best Android antivirus solutions available. It combines exceptional malware detection with one of the most complete sets of security and privacy tools on the market. The anti-theft features, in particular, stand out for their reliability and depth.
The app’s clean design, strong VPN, data leak checker, and customizable protections make it ideal for both casual and security-conscious users. We highly recommend Kaspersky for Android to anyone seeking dependable, feature-rich protection and robust privacy on mobile devices.
McAfee Review
#3 of 28 antivirus for Android
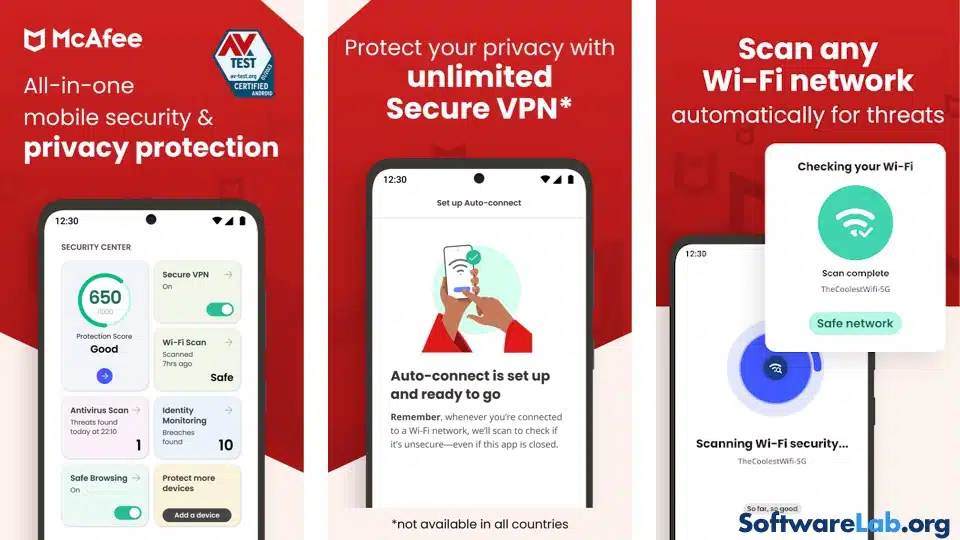
McAfee is #3 of 28 apps for Android.
McAfee has a beautiful design and covers most of the features we want in a security app. It includes anti-malware, AI powered anti-phishing, an identity theft scanner, and an unlimited VPN. But it lacks anti-theft tools, and its bonus features only include a Wi-Fi security checker.
Try it risk-free, thanks to its 30-day return policy.
Detailed Review
McAfee Antivirus for Android Review
Design and Layout
In our testing, McAfee Mobile Security for Android impressed us with its clean, modern interface and intuitive structure. The app is organized around three main tabs at the bottom of the screen, allowing easy navigation between its core functions. This design ensures users can quickly access essential tools without feeling overwhelmed, making it an excellent option for beginners and experienced users alike.
Educational and Actionable Insights
The first tab focuses on cybersecurity awareness. It provides concise, educational content explaining common mobile threats—such as the risks of connecting to unsecured Wi-Fi networks—and pairs this information with practical, easy-to-follow advice. Users are encouraged to take simple actions like enabling safe browsing or securing their connections, helping even non-technical users strengthen their digital safety.
Security Features
The second tab houses McAfee’s main protection tools, delivering reliable, real-time security across multiple threat vectors:
- Antivirus Scan: McAfee’s scanner efficiently detects and removes malware, ransomware, and other malicious content in apps, downloads, photos, and videos. Its real-time protection continuously monitors for threats, ensuring proactive defense without slowing the device.
- Identity Protection: Users can register personal information—such as email addresses and credit card numbers—for dark web monitoring. McAfee automatically checks for data breaches and alerts users if their details are found, offering vital protection against identity theft.
- Secure VPN: McAfee includes an unlimited VPN that encrypts all online traffic, maintaining privacy and anonymity while browsing. Unlike some competitors (for example, Bitdefender’s 200 MB/day limit), McAfee’s VPN has no data cap, making it ideal for frequent public Wi-Fi use.
- Wi-Fi Security Scanner: This feature evaluates the security of connected networks, confirming the strength of encryption and warning against unsafe or unprotected hotspots. It’s an essential safeguard for users who regularly connect to public Wi-Fi.
- Safe Browsing: The built-in anti-phishing and web advisor tools block access to malicious URLs and scam websites, preventing data theft and financial fraud during online browsing.
Is McAfee the Best Antivirus for Android?
McAfee Mobile Security delivers a strong combination of modern design, ease of use, and essential protection features. Its antivirus engine, dark web monitoring, VPN, and Wi-Fi tools create a well-rounded security package that performs reliably in real-world use.
However, while McAfee provides a polished and effective Android experience, competitors like Norton offer broader protection—particularly through additional tools such as password management, enhanced VPN features, and multi-device support.
For users seeking a straightforward, visually appealing, and dependable antivirus solution, McAfee Mobile Security is an excellent choice. But for those looking for a more advanced and versatile suite, Norton 360 remains the stronger all-around option.
Bitdefender Review
#4 of 28 antivirus for Android

Bitdefender is #4 of 28 apps for Android.
Bitdefender Mobile Security for Android covers all the core features: Anti-malware, web protection, anti-theft tools, an identity theft scanner, and a VPN.
However, it can’t match the Android apps of Norton or Kaspersky.
Norton and Kaspersky have a more comprehensive range of security features, a better design, and a no data limit on their VPN.
Unless you’re a big fan of the Bitdefender brand, we believe Norton and Kaspersky are better Android antivirus apps.
Try it risk-free, thanks to its 30-day return policy.
Detailed Review
Bitdefender Antivirus for Android Review
Overview
In our hands-on testing, Bitdefender Mobile Security for Android delivered excellent protection and reliable performance. While it doesn’t have the same visual refinement as Norton or McAfee, it compensates with a strong suite of security tools and consistently high malware detection rates. Its focus is on function over form—making it a dependable, if slightly utilitarian, choice for users who value substance over style.
Dashboard
Bitdefender’s interface is minimalist but straightforward. The Dashboard provides direct access to essential tools like Scam Alert, App Lock, Web Protection, and Anti-Theft. Once these features are activated, the app displays a reassuring green “Protected” status. Although the design lacks flair, the layout is clean, uncluttered, and efficient—ideal for users who prioritize practicality and quick access to core functions.
Malware Scanner
During testing, Bitdefender’s Malware Scanner proved exceptionally accurate. It swiftly detected ransomware, adware, spyware, and even cryptomining malware with minimal impact on performance. The scanner thoroughly checks all installed apps and files, ensuring full system coverage. Bitdefender’s real-time protection operates quietly in the background, maintaining continuous defense without draining battery life.
Web Protection
Bitdefender’s Web Protection integrates seamlessly with popular browsers such as Chrome, Firefox, and Opera, blocking phishing links and malicious websites before they can cause harm. Its cross-browser compatibility ensures users stay protected no matter which browser they prefer, providing a smooth and secure online experience.
Scam Alert
The Scam Alert feature scans incoming SMS messages for phishing attempts, warning users about links or content that could lead to scams. With the growing number of SMS-based frauds, this proactive protection adds meaningful value for everyday mobile users.
Additional Features
- VPN: Bitdefender includes a built-in VPN that encrypts web traffic for secure browsing, but it’s limited to 200 MB per day. Users who need unlimited VPN access can upgrade to Bitdefender’s dedicated VPN service. By comparison, Norton and Kaspersky include unlimited VPNs in their premium plans.
- Anti-Theft: The anti-theft suite allows remote location tracking, device locking, and data wiping. It also snaps a photo with the front camera after three failed unlock attempts, helping identify potential intruders.
- Account Privacy: This tool monitors for data breaches and alerts users if their personal information—such as email addresses or passwords—appears on the dark web.
- App Lock: Bitdefender lets users secure sensitive apps with a PIN or biometric authentication. This is particularly useful for safeguarding banking, messaging, and social media apps from unauthorized access.
Is Bitdefender the Best Antivirus for Android?
Bitdefender stands out for its excellent malware detection, smooth performance, and effective web and anti-theft protection. However, its VPN limitations and somewhat plain interface make it less appealing than feature-rich competitors like Norton, which combines unlimited VPN access and a more refined design.
For users who value straightforward, high-performance protection and don’t rely heavily on VPN use, Bitdefender Mobile Security remains a strong, trustworthy option. But for those seeking a more polished experience with broader functionality, Norton 360 continues to set the benchmark for Android security.
Panda Review
#5 of 28 antivirus for Android

Panda is #5 of 28 apps for Android.
Panda free antivirus for Android includes anti-malware, a VPN with a 150 MB / day data limit, anti-theft, a call blocker, an app locker, and a permissions scan. Especially the last one, the permissions scan, is a rare feature we would like to see more often in other antivirus apps.
However, if you’re willing to spend a few dollars, Norton offers better protection for users who frequently use public Wi-Fi networks, thanks to its unlimited VPN.
Try it risk-free, thanks to its 30-day return policy.
Detailed Review
Panda Antivirus for Android Review
We tested both the free and premium versions of Panda Dome Antivirus for Android, evaluating their protection capabilities, performance, and overall user experience. While Panda provides solid core security features—especially in its free tier—its premium version offers several useful upgrades for enhanced privacy and theft protection.
Free Version Features
- Antivirus: Panda’s malware scanner supports both manual and automatic scans of apps, files, and SD cards. Users can also schedule regular scans for ongoing protection. In our testing, it consistently detected and removed common Android threats quickly and efficiently.
- VPN: The free plan includes a VPN limited to 150 MB per day, which is sufficient for light tasks such as checking email or browsing securely on public Wi-Fi. However, it’s too restrictive for streaming, downloading, or extended use.
- Privacy Auditor: This tool reviews app permissions, identifying which apps access sensitive data such as location, contacts, or media. It allows users to uninstall intrusive apps directly, offering clear control over data privacy.
- Anti-Theft: The free version includes essential anti-theft tools for locating, locking, or remotely wiping a lost or stolen device—valuable features for users concerned about mobile security.
Paid Version Additions
- Advanced Anti-Theft: The premium plan enhances theft protection with additional options such as remotely triggering alarms or taking a photo using the front camera after failed unlock attempts. These features can help identify or deter potential thieves.
- Call Blocker: Allows users to block specific numbers—including hidden or unknown callers—reducing spam calls and boosting privacy.
- App Lock: Adds an extra layer of security by protecting selected apps (like banking or social media) with a 4-digit PIN, preventing unauthorized access to sensitive information.
Conclusion: Is Panda the Best Antivirus for Android?
Based on our hands-on testing, Panda Dome Antivirus delivers impressive protection and functionality for a free app. Its malware detection, basic VPN, privacy controls, and anti-theft tools make it one of the strongest free Android antivirus options available.
That said, its limitations—particularly the VPN’s small data cap and lack of advanced web protection—mean it falls short of premium alternatives. Competitors like Norton and Kaspersky offer more comprehensive suites, including unlimited VPN access, stronger anti-phishing safeguards, and a smoother overall experience.
In summary, Panda Dome is an excellent choice for users seeking free, reliable antivirus protection with essential tools. However, those who need advanced, all-in-one mobile security will find better long-term value in paid options like Norton or Kaspersky.
Specification comparison
Below, we compare some of the best antivirus of 2026.
The core features we look for are anti-malware, anti-phishing (web protection), anti-theft, identity theft scanner (dark web monitor), and an unlimited VPN.
The anti-malware scores are based on our own in-house tests and the protection test scores for Android by AV-Test, the independent test lab from Germany. The speed impact scores are based on the performance test scores for Android by AV-Test.
Sadly, Panda does not partake in the trial runs of AV-Test. Therefore, we have no objective data to judge its anti-malware protection and speed impact.
Test score comparison
We conduct in-house anti-malware tests and review the results from AV-Test, a German lab renowned for its objective evaluations. Below is the average of the last 10 AV-Test results for Android. Their scoring criteria are:
- Protection (1-6): Effectiveness in blocking malware.
- Performance (1-6): Impact on system speed.
- Usability (1-6): Frequency of errors like false alarms.
We calculate a final score using this formula:
Final Score = 60% Protection + 20% Performance + 20% Usability.
While these results influence our of the best antivirus app for Android, other factors like privacy and identity protection also play a key role. For a similar analysis for Windows or macOS, visit our other comparisons:
Note: Brands not listed in the table either do not participate in AV-Test trials or are tested too infrequently, such as Surfshark or Panda.
Source: AV-Test. Last Update: November 2025.
User reviews
We’ve compared the user reviews of all antivirus brands. We’ve used the scores and review count of TrustPilot, a leading user review platform.
We consider scores above 4.0 very good. Lower scores indicate that the brand might have a poor product or customer service. McAfee’s scores, for instance, are worrying.
Source: TrustPilot. Last Update: November 2025.
Buying Guide
Common questions about antivirus software
How does antivirus software work?
Antivirus software identifies and eliminates harmful programs through various detection methods:
- Signature-based detection: Scans apps and files against a database of known malware signatures to detect existing threats.
- Heuristic analysis: Identifies new or modified malware by analyzing suspicious code or unusual structures.
- Behavioral detection: Monitors app behavior in real time to flag malicious activity such as data theft or unauthorized access.
- Real-time protection: Continuously scans downloads, app installations, and system processes to stop malware before it spreads.
- Machine learning and AI: Uses intelligent algorithms to detect emerging threats and adapt to evolving attack patterns.
For more, read our blog post on what antivirus software is.
What other features does antivirus have?
Modern antivirus programs offer more than basic malware protection, incorporating essential features like:
- Anti-phishing protection: Blocks fake websites and messages designed to steal login or payment information.
- Firewall: Controls network connections to prevent unauthorized access to your data.
- Password manager: Stores and encrypts passwords securely for easier and safer logins.
- VPN (Virtual Private Network): Encrypts your internet traffic and hides your IP address for privacy.
- Identity theft protection: Monitors personal data to alert you of leaks or misuse.
- Parental controls: Limits children’s access to apps, content, and online activities.
In summary, antivirus for Android is an essential layer of protection that helps safeguard your device from various online threats, with advanced tools that go beyond malware detection.
What cyber threats can antivirus protect you from?
Antivirus software for Android can protect users from a wide range of malware threats, including:
- Adware: Displays intrusive ads or redirects you to malicious websites.
- PUP (Potentially Unwanted Programs): Unwanted apps that slow down performance or collect personal data.
- Ransomware: Locks files or your device and demands payment for access.
- Rootkits: Hides malicious activity to maintain unauthorized system access.
- Spyware: Steals sensitive information like messages, contacts, and location data.
- Trojans: Masquerades as legitimate apps to install or execute malicious code.
- Viruses: Infects and corrupts files, spreading across apps and storage.
- Worms: Self-replicating malware that spreads automatically through networks.
Thanks to tools like anti-phishing, firewall, password manager, VPN, identity theft protection, and parental controls, modern antivirus suites can safeguard users from a wide range of cyber threats beyond just malware.
What cyber threats can’t antivirus protect you from?
Antivirus software for Android is highly effective against many malware threats, but it can’t protect you from social engineering attacks. These involve tricking users into sharing personal information or performing harmful actions, such as clicking malicious links or revealing login credentials—phishing scams and fraudulent phone calls are common examples.
Additionally, antivirus programs may not always catch zero-day attacks—new and unknown vulnerabilities exploited by hackers before the software can be updated. While many antivirus tools have advanced detection methods, they aren’t guaranteed to stop every zero-day threat immediately. Staying vigilant and keeping your software up-to-date is essential for the best protection.
What are the built-in security features of Android?
Here’s an overview of Android’s key security features and what they do:
- Google Play Protect: Automatically scans apps from the Play Store and your device for malicious behavior.
- Encryption: Protects stored data by encrypting it, ensuring only authorized users can access it.
- Security Updates: Regular system and app updates patch vulnerabilities and improve protection.
- Sandboxing: Isolates apps from each other to prevent unauthorized data sharing or access.
- Biometric Authentication: Uses fingerprint or facial recognition for secure and convenient access.
- Permissions Control: Lets users manage which apps can access sensitive data or features like location or camera.
- Find My Device: Helps locate, lock, or erase a lost or stolen phone remotely.
While these features are solid, they may not cover all your security needs.
What security features does Android lack?
Android lacks a few advanced tools that other platforms or third-party apps provide:
- Cross-OS Password Manager: Android lacks a native, cross-platform password management solution.
- VPN (Virtual Private Network): No built-in VPN for encrypted browsing and privacy protection.
- Identity Theft Protection: Doesn’t include tools to monitor personal data or alert users of breaches.
- Advanced Anti-Phishing Tools: Limited phishing protection in mobile browsers and messaging apps.
- Comprehensive Parental Controls: Google Family Link offers basic controls but lacks advanced monitoring features.
For basic device security, Android is robust. However, if you want more comprehensive protection, consider supplementing it with third-party tools or services.
How do we test antivirus software?
Anti-Malware Protection (30%)
We evaluate how well the antivirus detects and removes various malware types like viruses, trojans, ransomware, and spyware.
- In-House Testing: Using 1,200 diverse malware samples, we conduct real-time attack simulations to assess detection and neutralization of known and emerging threats through signature-based and heuristic analysis.
- Independent Lab Results: We incorporate findings from respected institutes like AV-Test, SE Labs, and AV-Comparatives to validate our results.
Security and Privacy Features (30%)
We assess additional tools that enhance cybersecurity:
- Web Protection: Testing the software’s ability to block phishing sites and web-based threats by accessing known malicious websites.
- Firewall: Evaluating effectiveness using intrusion simulations and the ShieldsUP! test to secure network ports and monitor traffic.
- Password Manager: Assessing capabilities to generate, store, and auto-fill complex passwords, plus features like two-factor authentication and biometric login.
- VPN: Evaluating security protocols, encryption, speed, server locations, data limits, and support for streaming and peer-to-peer sharing while hiding IP addresses.
- Parental Controls: Testing screen time management, content filtering, location tracking, and resistance to bypass attempts to protect children.
- Identity Theft Protection: Assessing monitoring of personal info and responsiveness to potential identity theft alerts.
- Secure Cloud Storage: Evaluating capacity, security, usability, and features like file encryption and secure sharing.
- Anti-Ransomware: Simulating attacks to test detection and blocking of unauthorized encryption via behavioral detection and exploit prevention.
- Dark Web Monitoring: Checking effectiveness in scanning the dark web for personal info and providing timely alerts.
System Performance Impact (10%)
We measure how the antivirus affects device performance during everyday tasks:
- Resource Usage: Monitoring CPU and memory during scans and real-time protection.
- Performance Tests: Evaluating impact on launching apps, downloading files, browsing websites, and copying data, aligned with AV-Test criteria.
False Positives (10%)
Accuracy is crucial to avoid interruptions:
- False Positive Detection: Assessing how often legitimate applications or files are incorrectly flagged.
- Usability Tests: Referencing AV-Test evaluations to gauge false positive frequency for effectiveness and user-friendliness.
Price and Value (10%)
We analyze overall value by comparing features to cost:
- Cost Analysis: Considering subscription prices, device coverage, and multi-year plans.
- Feature Evaluation: Assessing if included features justify the price compared to competitors.
Ownership and Reputation (10%)
Trust is essential in cybersecurity providers:
- Company Background: Researching history, industry track record, mergers, or acquisitions.
- Privacy Policies: Examining data handling, privacy commitment, and compliance with regulations.
- Ethical Conduct: Investigating past unethical behavior, data breaches, or controversies.
Sources and tools
Below are the sources and tools we’ve used to test the antivirus software:
- Apple Platform Security
- AV-Comparatives Consumer
- AV-Test Android
- AV-Test macOS
- AV-Test Windows
- GRC Firewall Test
- Microsoft Defender
- SpeedTest VPN
- Trustpilot Security Software
Read more about how we test antivirus software.
What software have we tested?
We have tested 39 antivirus software from 28 brands. These range from free antivirus programs, to entry-level paid antivirus programs, mid-range paid antivirus software, and full-featured internet security suites.
These are the programs we recommend:
- Norton Antivirus Plus
- Norton 360 Standard
- Norton 360 Deluxe
- Norton 360 Advanced
- Norton 360 for Gamers
- Norton Antivirus for Mac
- Avast Antivirus One
- TotalAV Antivirus
- Bitdefender Antivirus Plus
- Bitdefender Internet Security
- Bitdefender Total Security
- Bitdefender Premium Security
- McAfee Antivirus LiveSafe
- McAfee Total Protection
- Panda Dome Antivirus
- Avira Antivirus Prime
- Surfshark Antivirus
- Intego Antivirus
- Kaspersky Antivirus Standard
- Kaspersky Antivirus Plus
- Kaspersky Antivirus Premium
- AVG Antivirus
We believe that Norton Antivirus Plus is the best entry-level antivirus software and Norton 360 Deluxe the best antivirus all around.
If you have a specific operating system that you would like to protect, we probably have a dedicated antivirus comparison for it:
- The best antivirus of 2026 – For all OS.
- The best antivirus for Windows 11 – For Microsoft’s latest desktop OS.
- The best antivirus for macOS – For Apple’s desktop OS.
- The best antivirus for Android – For Google’s mobile OS.
- The best antivirus for iPhone – For Apple’s mobile OS.
- The best antivirus with a VPN – For both security and privacy.
- The best antivirus with a Firewall – For a focus on network security.
- The best VPN of 2026 – For a dedicated privacy solution.
Click the links to be taken to your comparison of choice.
Does this page exist in other languages?

Author: Tibor Moes
Founder & Chief Editor at SoftwareLab
Tibor has tested 28 antivirus programs and 25 VPN services, and holds a Cybersecurity Graduate Certificate from Stanford University.
He uses Norton to protect his devices, NordVPN for his privacy, and Proton for his passwords and email.
Save on the best antivirus of 2026:
🥇 Norton Antivirus (70% off) 🔥
🥈 Kaspersky Antivirus
🥉 McAfee Antivirus
